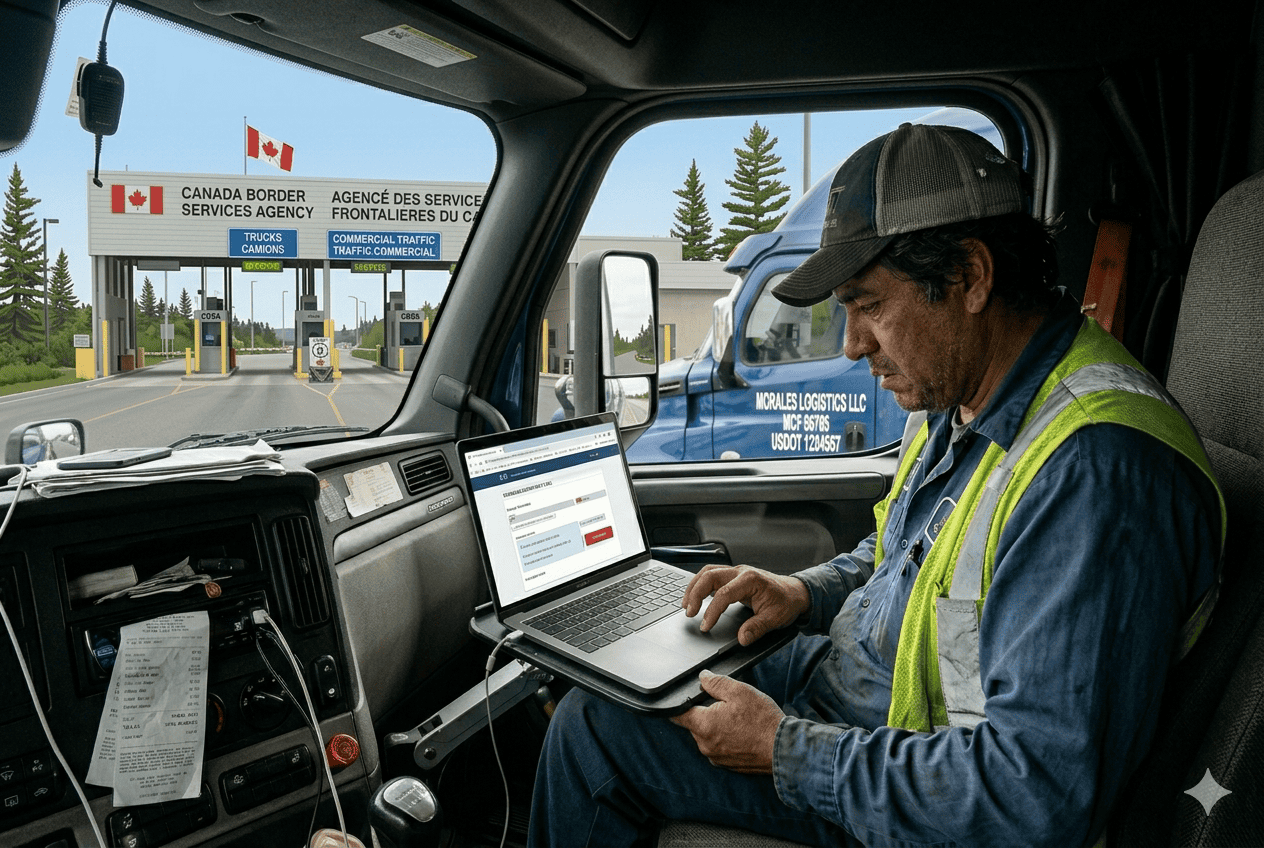
Are trucks now vulnerable to sabotage by virtue of the information systems that once amazed drivers?
The answer is yes, if truck owners don’t take steps to address the threat – and if OEMs don’t take it into account when they design and manufacture new vehicles.
We’re talking about the threat to assets that comes specifically through truck diagnostic systems.
During a recent interview with FreightWaves, the National Motor Freight Traffic Association’s (NMFTA) Senior Cybersecurity Research Engineer Ben Gardiner discussed this issue (and many others) on a FreightWavesNOW segment. View Ben’s interview with Kaylee Nix here.
History of Diagnostic Systems
On-board diagnostics were an eyebrow-raising innovation for cars and trucks when first introduced in the 1970s, and when they broke through full-force in the 1980s.
The motor vehicle at that time was only a few decades old as a mainstream form of transportation, and it was revolutionary to consider that the vehicle itself could detect there was something wrong with it – and could tell you about it.
The first all-out OBD system was standard on the 1980 Cadillac Eldorado and Cadillac Seville, which displayed diagnostic trouble codes to drivers. Over the course of the next several years, GM upgraded the systems to include a Computer Command Control system as standard on all passenger vehicles.
Drivers came to recognize certain notifications, such as “Check Engine Light” or “Service Engine Soon.” Over the course of the next several decades, the systems became more sophisticated and easier for drivers to use. OBD systems became increasingly used by vehicle telematics devices that perform a variety of functions.
Truck fleets pioneered many steps forward, especially through innovations like electronic data interchange (EDI).
But while the uses became more sophisticated, for the most part, many of these systems were run via AS400 Operating Systems. These are mid-range server systems developed by IBM, and first released in 1988. To give the AS400 its due, the system is still in demand today by many small and medium-sized organizations. It has stood the test of time in situations where it’s used properly.
However, AS400 systems were never designed to account for threats that might come via the internet. That was not a problem until internet-connected devices came into the picture.
In Walks The Internet
Car and truck diagnostic systems of the 1980s and 1990s were designed to deliver high up time and high reliability. They contained control loops that would ensure the diagnostic systems would do mostly whatever they were told to do when someone sent them a message.
At the time, this is exactly what everyone wanted. After all, only those in control of the vehicle would have any reason or opportunity to give the system commands. There was no such thing as a popularly utilized internet, and there was certainly no such thing as internet-connected devices that could be used by hackers to take control of a vehicle’s diagnostic system and sabotage it.
For these reasons, cybersecurity was not a consideration during the early development of truck diagnostic systems. The systems were never designed to be on, or connected to, the internet.
Today things are very different. Platforms like electronic logging devices (ELDs), for example, have their own cyber vulnerabilities, and NMFTA has developed extensive recommendations for how to secure ELDs in the cyber environment.
Protecting Your Vehicles
While there are no significant known incidents of truck attacks or truck ransomware, the industry needs to stay ahead of the curve. We believe the top security priorities for the industry should be:
1. The security of telematics devices. These are the hacker’s initial foothold into the system, and it’s essential that they remain secure.
One problem with ELDs is that there are so many providers in the market—hundreds at last count—and far too many are not sufficiently secure. Quite a few have gone out of business in recent years, and that’s useful because there’s a need to cull the herd. But the market is still huge and buyers need to beware before they work with any ELD provider.
2. Segmentation and separation of truck networks from the telematics devices. This is simply another layer of security so that, if a hacker does manage to breach the telematics device, he or she won’t be able to use it for easy access to the rest of the assets and/or the enterprise.
NMFTA has also developed a questionnaire fleets and truck owners can use to assess the cybersecurity strength of their telematics providers, since you don’t want to take all these steps only to find that you’ll end up exposed anyway by a careless telematics provider.
Gardiner will also be leading the hacking of a tanker truck at our upcoming Digital Solutions Conference on Cybersecurity, which will be held in Houston, TX from October 22-25. Learn more about the hack via our Commercial Carrier Journal column.
We need to protect our industry’s assets. They have held up remarkably well to date, but the vulnerabilities are real and we have to take them seriously.